This is an old revision of the document!
RADIUSdesk Wireguard Agent
Overview
- The RADIUSdesk Wireguard Agent is a lightweight add-on to Ubuntu or Raspberry Pi devices that serves as a broker between Wireguard and RADIUSdesk.
- It uses a couple of Lua based libraries and scripts to fulfill its mandate.
Installation
Please double check
- Make sure the iptables package is installed. (It was not installed on my Raspberry Pi OS image)
sudo apt-get install iptables
- Make sure packet forwarding for IPv4 is enabled. Edit the /etc/sysctl.conf.
- Find and uncomment net.ipv4.ip_forward=1 line.
- Apply all sysctl settings (recommended)
sudo sysctl -p
The Rest
- Make sure the Wireguard package is installed.
sudo apt update sudo apt install wireguard
- Install the following packages.
sudo apt-get install -y curl lua-socket lua-cjson luarocks sudo luarocks install inifile
- Check out the latest RADIUSdesk code
cd /var/www sudo git clone https://github.com/RADIUSdesk/rdcore.git #Link the wireguard agent's files to /etc directory. #The accel-ppp folder is correct and part of the history of the project sudo ln -s /var/www/rdcore/cake4/rd_cake/setup/accel-ppp/MESHdesk /etc/MESHdesk
Configuration
Startup and config reference files
- Copy the following reference files:
#config file for the agent sudo cp /etc/MESHdesk/files/wireguard-rd.conf /etc/ #startup file. We make a backup first of the original one (of there were one) cp /etc/rc.local /etc/rd.local.bak sudo cp /etc/MESHdesk/files/rc.local /etc/
Config File
- Configuration is done by tweaking the /etc/accel-ppp-rd.conf file.
- Refer to the sample below.
- Here we run Wireguard on the same server as RADIUSdesk so we can specify 127.0.0.1 for IP Address.
[internet] disabled=0 dns=cloud.radiusdesk.com url=cake4/rd_cake/nodes/get-config-for-node.json status_url=cake4/rd_cake/node-reports/submit_report.json actions_url=cake4/rd_cake/node-actions/get_actions_for.json protocol=https http_port=80 https_port=443 ip=127.0.1.1 interface=eth0 [wireguard] interface=eth0
- In our setup we have a RADIUSdesk server which has a FQDN of cloud.radiusdesk.com
- We also specify the fallback ip as 127.0.0.1 in the event when DNS does not resolve.
- Protocol can be either https or http. We choose https which is more secure.
- We also specify the interface we want the Wireguard service to run on.
- In our case we have a VPS with an Enternet port (eth0) where we will run Wireguard on.
- The agent will then fetch the MAC Address of this interface and forward the request for config to RADIUSdesk using this MAC Address as the unique identifier.
- Make changes to this file so that it works with your environment and device.
Startup File
- Disable automatic startup of Wireguard.
sudo systemctl disable wireguard
- The startup file is /etc/rc.local.
- You also have to tweak it to work on the device running the RADIUSdesk Accel-ppp Agent.
- Refer to the sample below
#!/bin/bash iptables -t nat -A POSTROUTING -o wlan0 -j MASQUERADE cd /etc/MESHdesk sleep 10 /etc/MESHdesk/u.lua & sleep 10 /etc/MESHdesk/heartbeat.lua & exit 0
- The important line is the one with the iptables rule for NAT.
- With our setup the WAN connection / uplink is the WiFi interface, wlan0.
- Make sure that your setup matches your device's configuration.
Since PPPoE works on Layer2, you can have both the PPPoE and the WAN connection on one physical interface e.g eth0 in our case with the Pi.
- On the Raspberry Pi the rc.local script was called automatically during startup.
- On Ubuntu you'll probably have to follow these instructions to ensure that it starts up during boot time
- Everything should now be in place and you can reboot the device and see if it is listed under Accel-ppp Servers → New Arrivals
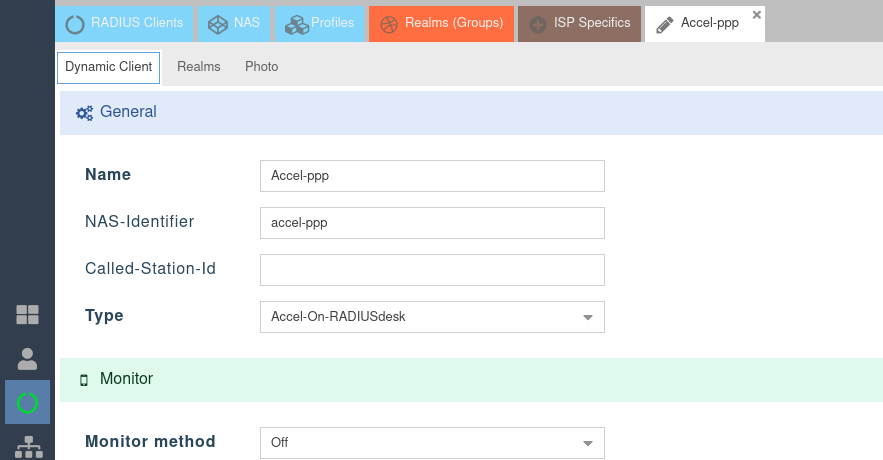
RADIUS Client
- If your Accel-ppp server is using RADIUSdesk for its RADIUS component you have one last step to do.
- You can do its RADIUS on-boarding by looking for it under RADIUS → RADIUS Clients → New Arrivals.
- After you completed the on-boarding be sure to specify the Client Type as Accel-On-RADIUSdesk.
- This will allow the code to follow the correct procedure when an active session for a user needs to be terminated.